MENA’s governments and organisations have fallen victim to some of the most infamous cyber-attacks in history.
Looking back at the region’s last 10 years of disruptions reveals the frightening potentials of cyber warfare: malware are becoming bolder, their consequences more damaging, and their occurrences more frequent. Here is a review of five malware to have been used against MENA’s infrastructure and to have marked the world’s cyber war history:
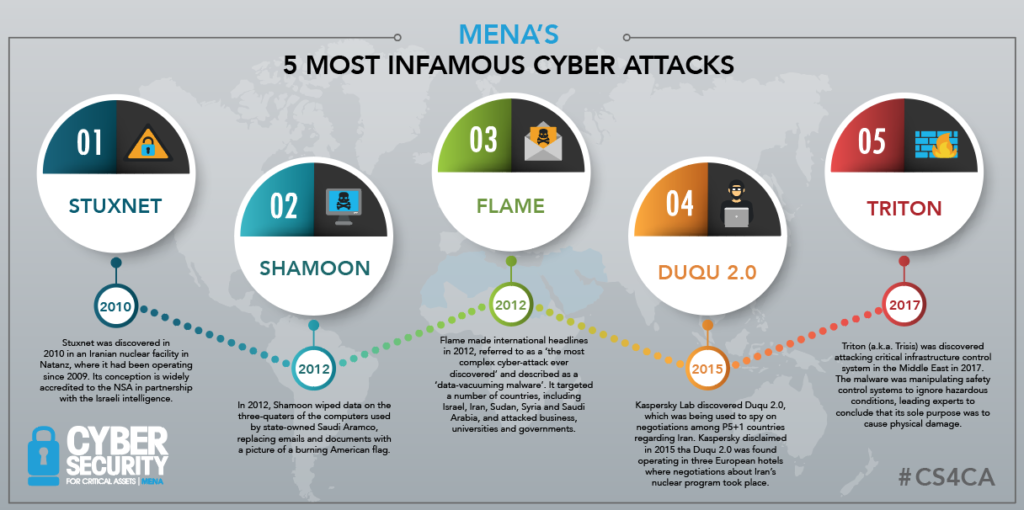
1) Triton
Triton (a.k.a. Trisis) was discovered attacking critical infrastructure control systems in the Middle East in 2017. The malware was manipulating safety control systems to ignore hazardous conditions, leading experts to conclude that its sole purpose was to cause physical damage.
Because of its violent intent, Triton has been described as “the next generation of cyber weaponry” and as “a tool so dangerous that its mere existence significantly intensifies the global digital arms race.” Luckily, instead of achieving its destructive objective, Triton triggered the safety system’s emergency shutdown procedure that it was trying to repress, revealing its own existence. This is the third-ever known malware specimen focused on damaging or disrupting physical equipment.
The first is:
2) Stuxnet
Stuxnet was discovered in 2010 in an Iranian nuclear facility in Natanz, where it had been operating since 2009. Its conception is widely accredited to the NSA in partnership with the Israeli intelligence.
Natanz is a Fuel Enrichment Plant, an underground uranium enrichment facility protected by a concrete wall 2.5 meters thick, itself protected by another concrete wall. But cyber-attacks know no such boundaries: security firm Symantec disclosed that Stuxnet penetrated the nuclear facility through an infected USB stick. Once inserted into a computer attached to the network, Stuxnet uploaded itself into the system and hunted for the software that controls the plant’s centrifuges.
Designed to cause continuous damage rather than a one-hit strike, Stuxnet manipulated machines for months towards self-destruction: it made the centrifuges’ rotors spin too fast and too slowly, alternately, for several minutes at a time before returning to normal speed. A thousand machines were destroyed as a result, causing Natanz to decommission around 20% of its centrifuges, estimated the BBC.
This episode was the first to alert the world to the dangers of cyber-attacks – it became clear that their consequences aren’t limited to the digital realm and can have serious physical impacts.
3) Shamoon
In 2012, Shamoon wiped data on three-quarters of the computers used by state-owned Saudi Aramco, replacing emails and documents with a picture of a burning American flag.
This malware is a multipurpose tool that spreads on local network using stolen administrator credentials. Shamoon was launched on the eve preceding a Muslim holiday, acting unnoticed all weekend while the company’s 55,000 employees were at home. This attack has been credited to Iran by the USA, seen as retaliation for the previously mentioned Stuxnet.
A version of Shamoon returned four years later to attack Saudi Arabia’s civil aviation agency and other Gulf State organisations. On the 2016 incident, computer screens displayed a disturbing photo of three-years-old Syrian refugee Alan Kurdi, who had drowned in the Mediterranean the year before. While the motive behind Shamoon’s return wasn’t clear to the Symantec Security Response team, they disclosed their only certainty: “the attackers want their targets to sit up and take notice.”
4) Flame
Flame made international headlines in 2012, referred to as a “the most complex cyber-attack ever discovered” and described as a “data-vacuuming malware”. It targeted a number of countries, including Israel, Iran, Sudan, Syria, Lebanon, Saudi Arabia and Egypt, and attacked businesses, universities and governments.
In 2012, the year in which Kaspersky Lab discovered the virus, Eugene Kaspersky spoke at a cyber conference in Israel: “I’m afraid it’s just the beginning of the game. I’m afraid it will be the end of the world as we know it. I’m scared, believe me.” Kaspersky told the BBC that Flame had been operating since at least August 2010. That’s two years before it was discovered: Flame has the capacity to identify which anti-virus software is used by its host machine and modify its behaviour accordingly, to avoid detection.
As if that wasn’t scary enough, Itp.net lists other things Flame can do, including: “steal documents, take screenshots of users’ desktops, spread via USB drives, disable security vendor products, turn on PC microphones and Bluetooth and search for nearby devices, intercept network traffic, and record Skype conversations.” In other words, Flame differs from other malware in its refined ability to receive and pass on information through the ‘eyes and ears’ of a computer.
5) Duqu 2.0
Kaspersky Lab discovered Duqu 2.0, which was being used to spy on negotiations among P5+1 countries regarding Iran. Kaspersky disclaimed in 2015 that Duqu 2.0 was found operating in three European hotels where negotiations about Iran’s nuclear program took place.
Duqu 2.0 exploits up to three zero-day vulnerabilities at a time and is believed to be a variant of the Duqu worm; itself a variant of Stuxnet. Israel is thought to have deployed the original Duqu to carry out sensitive intelligence gathering, wrote The Guardian in 2015, but the threat actor behind Duqu 2.0 wasn’t revealed.
Duqu 2.0 shocked the world also because it attacked the cyber security experts themselves. Eugene Kaspersky commented on the incident: “Spying on cybersecurity companies is a very dangerous tendency. Security software is the last frontier of protection for businesses and customers in the modern world, where hardware and network equipment can be compromised. Moreover, sooner or later technologies implemented in similar targeted attacks will be examined and utilised by terrorists and professional cybercriminals. And that is an extremely serious and possible scenario.”
#
CS4CA MENA is a content-driven platform uniting the region’s senior security leaders to learn, discuss and assess the practical steps needed to achieve cyber resilience. MENA’s Cyber Security for Critical Assets Summit takes place in Dubai, January 21st-22nd 2019. Secure your 2-day conference pass with a 25% discount with code MENA25 at www.cs4ca.com/mena/



